Home Blog
News
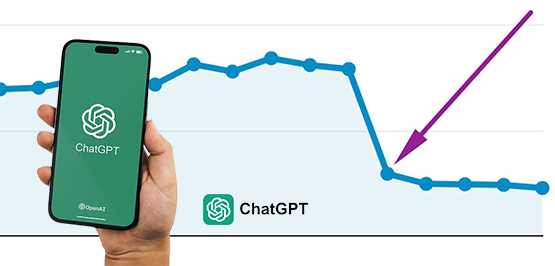
ChatGPT’s Traffic Decline Raises Questions about the Future of Generative AI
Saniya Chipolkar - 0
ChatGPT, a groundbreaking AI chatbot, caught everyone’s attention when it was launched in November. Its success led tech giants to adopt generative AI rapidly, CEOs to evaluate labor needs, and AI stocks to rally. With its human-like responses, ability to generate code and essays, and even pass professional tests, ChatGPT was hailed as the next big thing, integrated into...
A number of factors, including inflation and pressure to boost income following a break in price increases during the pandemic period, contributed to Salesforce’s decision to execute its first price rise in seven years in the ever-changing landscape of the technology business. As inflation has increased operating costs, the technology sector has seen a general increase in software prices,...
In a move that has been eagerly anticipated, tech billionaire Elon Musk has officially unveiled his ground-breaking artificial intelligence startup, xAI. With a mission to understand the true nature of the universe and develop a safer, fairer AI system. Musk aims to challenge the dominant players in the AI space, including OpenAI, Google, and Anthropic, comprising a team of...
Meme marketing is currently trending on social media platforms as it is incredibly efficient at informing your audience about a subject. The meme is a very cost-effective way of spreading the details related to your products and service. This marketing strategy is also great for boosting brand value and helping you reach a large audience.
What Do You Mean By...
Articles
How to Protect Your Martech Stack From Cyber-Attacks: 5 Tips and Strategies for Marketers
Sarrah Hizam - 0
In the modern business world, many marketing campaigns are run digitally. Using data-driven marketing strategies is one of the best ways to ensure success in those efforts. That’s why martech stacks of tools used to measure and optimize marketing campaigns are so useful.
But how do you protect company and customer data when using these tools? Here are our top...
Customers in the Middle East are very conscious of the quality and uniqueness of the content they get on their respective websites. Customers keep hopping from one web page to another in search of the content that they want from the webpage.
Not only the content, but the webpage ambiance, how interactive and user friendly is the webpage/site? It also...
Advertising Strategy
Inbound Marketing Strategies and Channels for Middle East Businesses
Sarrah Hizam - 0
Consumers do not like to have an inbox stuffed with promotional emails from brands to which they never subscribed or get advertisement popups. These mass marketing strategies are no longer as effective as they were once. Customers now choose what to purchase, who to purchase from, and whether or not to receive advertising. This defines why companies are adopting...
Advertising Strategy
How Loyalty Programs are a must for E-commerce in the Middle East
Sarrah Hizam - 0
Introduction to Customer Loyalty Programs
Today's digital consumers are significantly more discerning, aware of what they desire, and intolerant of poor customer service. Therefore, the retailers are in the driver's seat: it is up to them to determine what their customers want, what will make them happy, and what will keep them returning for more.
Marketers across all industries rely heavily...
Advertising Strategy
Top 10 Ways How Marketing Automation Can Help E-Commerce Businesses in the Middle East
Sarrah Hizam - 0
The Middle East has one of the youngest populations in the world. More than 28% of the Middle East's massive population of 108 million people are between the ages of 15 and 29. This is highly common in Egypt, Iraq, Lebanon, Morocco, Oman, Tunisia, Jordan, Algeria, and Saudi Arabia, where almost 20% of the population is between the ages...
Advertising Strategy
4 benefits of why is Native Advertising Important for Paid Marketing?
Sarrah Hizam - 0
Technology has altered the way consumers discover, assess, and purchase goods and services, ultimately elevating the significance of digital marketing. Today, companies are using digital marketing techniques to make the consumer aware of their product, customer acquisition, and increase their product's reach to various market segments.
Introduction to Native Advertising
Advertising a product and its information using ads on publisher's websites...