What is The Cyber Kill Chain Framework? What are its stages?
Cyber Kill Chain is a seven stage cyber-attack process and in turn, a defence model used in the identification and prevention of cyber-attacks on a computer network. This framework was first developed by the team at Lockheed Martin using the military attack models.
The Cyber Kill Chain model is the cybersecurity attack and defence model underpinning cyber intrusion detection solutions. In this framework, the attacks start with email phishing, advanced persistent threats enter into exploitation with malware binaries to gain access to network resources like credentials (fuzzing) then brute force password cracking happens on credentials that have been gathered in the previous stage of cyber attack chain trajectory.
The target applications get compromised through the exfiltration of data based on credentials that have been gathered in the previous stage of the cyber kill chain attack trajectory. Fewer intrusions related to malware detection and exfiltration data loss prevention are performed by the attacker during the phishing phase, leading to access to further network resources such as target information systems.
The Cyber Kill Chain consists of 7 stages, each stage demonstrates a specific goal along the attacker’s path. Each stage is required to achieve the next one. The Cyber Kill Chain is a model for understanding how an attack can affect the overall functioning of an organisation. Each stage in the chain presents a risk that must be mitigated before it can happen. Understanding the chain helps to identify what happened when an attack occurred so that it doesn’t happen again.
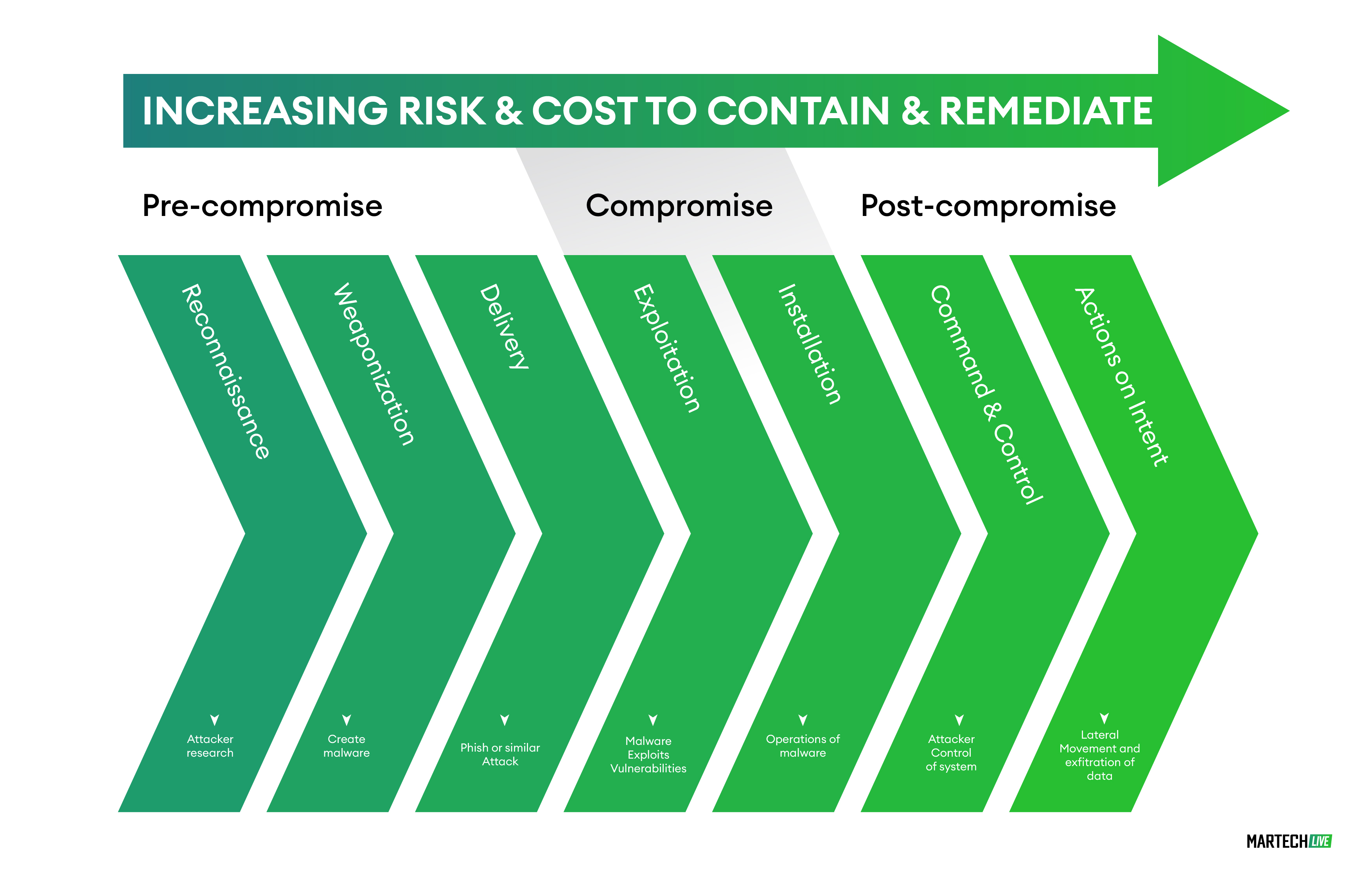
Stages of Cyber Kill Chain:
-
Reconnaissance:
This is the starting point- the information gathering stage. In this stage, the attacker chooses their target and conducts in-depth research on the target to identify its vulnerabilities and weaknesses.
-
Weaponization:
In this stage, the attacker creates a malware weapon like a virus, worm or other tools to exploit the vulnerabilities of the target. Generally speaking, weaponization depends on the target’s vulnerabilities and the attacker’s goal.
-
Delivery:
This stage involves transmitting the weapon to the target. The attacker can employ different methods such as phishing emails, social engineering methods, websites, compromised user accounts, USB drives etc.
-
Exploitation:
The malware is triggered to exploit the target’s weakness in order to gain key information and data.
-
Installation:
In this stage, attackers can install a malware code, modify security certificates or even install time bombs in the system. Whatever is installed in this stage depends on the attacker’s purpose and the vulnerabilities of the affected system.
-
Command and Control:
The attacker remotely controls and manipulates the target, thus the infected system falls into the hands of the attacker.
-
Actions on Objectives:
This is the last stage of The Cyber Kill Chain. The attacker achieves their goals such as data encryption for ransom, data theft (exfiltration) or data destruction.
How to break The Cyber Kill Chain?
While a cyber-attack is a very threatening situation for each company, there is some silver lining for professionals responsible to prevent them. For cyber attackers to be successful in their endeavour, they must go through each stage, however for the defensive teams, disrupting or stopping them at any point in the chain breaks The Cyber Kill Chain. Of course, the earlier it is detected and acted upon, the better results for security health. For example, if they cannot access a system/network, the attackers can never install the malware, naturally, they won’t be successful in taking control of the network.
Breaking The Cyber Kill Chain is vital to a company’s survival and success. Many measures can be taken at various stages, the earlier the better. Here are some points to consider to avoid a coordinated attack on your company’s network:
- Stopping Reconnaissance:
-
- Performing continuous inspection of network traffic to detect network scanning.
- Security professionals need to monitor and stop suspicious traffic with firewalls, IDS and IPS.
- Managing Hardware like Hard Disks properly.
- Limiting User access to sensitive databases and documents.
- Training users on all forms of social engineering attacks, such as phishing.
- Training users to limit what they post on social media, emails, hard drives etc.
- Stopping Weaponization:
-
- Stopping Reconnaissance would disrupt this stage, otherwise, it becomes very difficult to stop an attacker from executing this stage.
- Stopping Delivery:
-
- Configuring firewall, router ACL to block malware, risky websites, and inbound command-and-control communications.
- Installing anti-malware on both devices and network.
- Investing in Endpoint detection and response systems.
- Training users on the proper use of USB drives.
- Limiting users to download and install software and programs.
- Stopping Exploitation:
-
- Keeping systems and devices patched and updated.
- Training users to identify and report the signs of a malware infection.
- Stopping Installation:
-
- Limiting User’s account privilege.
- Separation of user privilege.
- Implementing strong passwords and enforcing password changes frequently.
- Enforcing two-factor authentication.
- Stopping Command and Control:
-
- Blocking outbound command and control communications.
- Blocking known malicious websites through URL filtering.
- Redirecting attacks to honeypot and honeynet.
- Stopping Actions on the Objectives:
-
- Proactively monitoring indicators of cyber-attacks on the network.
- Incident response.
- Strong support from Security providers.
How can Cybersecurity professionals put The Cyber Kill Chain model into practice?
The Cyber Kill Chain model can be used to inform the security and risk management process in a business. The goal is not just to prevent or mitigate cyber-attacks, but also to understand what happened when an attack occurs so that it doesn’t happen again.
Cybersecurity professionals should use this model as a guide for their actions if they are aware of one or more stages within the chain have been compromised on their network. The Cyber Kill Chain model can be used to inform the security and risk management process in a business. The goal is not just to prevent or mitigate cyber-attacks, but also to understand what happened when an attack occurs so that it doesn’t happen again.
The cyber kill chain model provides cybersecurity professionals with the knowledge and understanding of the security vulnerabilities to be tested within their network. The kill chain model gives cybersecurity professionals the information needed to further understand what has happened if an attack occurs, thus customizing the security and risk management process for each organization in order from least sensitive data collection to intrusion response.
Understanding how a cyber-attack can affect the overall functioning of the organisation is very important before readying the defence against it. As of now, more than 90% of cyber-attacks start with a random search to find a victim. These attempts are usually mass scale phishing attempts or the more sophisticated spear phishing. Usually, the attackers just prompt the victim to install the malware, and shockingly, the results of such mass scale activity are very effective. Hence, educating the entire workforce on the IT protocols and strict adherence to them is of paramount importance.
To be able to defend against cyberattacks, an integrated cyber protection system must be looked into. The construction of cyber security for any organisation must be viewed as a continuous process rather than just buying a technical solution. It is important to use all the tools available in the organisation and the support of a strong solutions provider to mitigate the risk of an attack.
Cybersecurity professionals use the Cyber Kill Chain model to combat breaches and minimize risks. The kill chain is a process that helps identify hackers, assess the damage, and respond to in-progress attacks. Knowing how hackers work allows us to select the right tools and strategies for limiting breaches, responding to in-progress attacks, and mitigating risks.
Cybersecurity is a dynamic field, and it evolves in ways that are unexpected, and surprising to technology companies. For example:
Artificial intelligence makes cyberdefenses more effective by learning from past attacks at the network level and reporting any changes to the organization. A real-time model of everyone’s work helps security professionals detect activity on mobile devices to ensure they’re connected wirelessly while avoiding spoofed or virtual access points backscatter networks. Machine learning technologies use building blocks to look for signs of emerging risks, responding in minutes rather than hours to new threats. A central security analysis tool created by a research and exploration staff can help organizations quickly sift through millions of logs from an organization’s IT infrastructure and detect any intrusions—in real-time.
Final Thoughts
As we go further in the digital age, more companies will be falling prey to vicious cyber-attacks. We cannot discount an individual in an organisation being compromised and exposing the entire network of the organisation to the imminent threat. Relying on preventive measures is alone not enough in such cases, as they are always one step behind the attackers.
Cybersecurity involves both prevention and mitigation of such an attack with minimal to no damage to the rest of the network. Modern solutions in the form of Endpoint security is very important for organisations to invest in to make sure their risk to such exposure is minimal. Also, very important for system administrators is to understand the Trends in Cybersecurity and stay up to date with the latest updates and patches offered by security providers.
As a cybersecurity provider, you may want to check out the report on Cybersecurity Market published by our partner- Straits Research, to understand the overall market dynamics, trends and potential opportunities to tap in.
Please subscribe to our Newsletters to receive such researched content right in your inbox.
